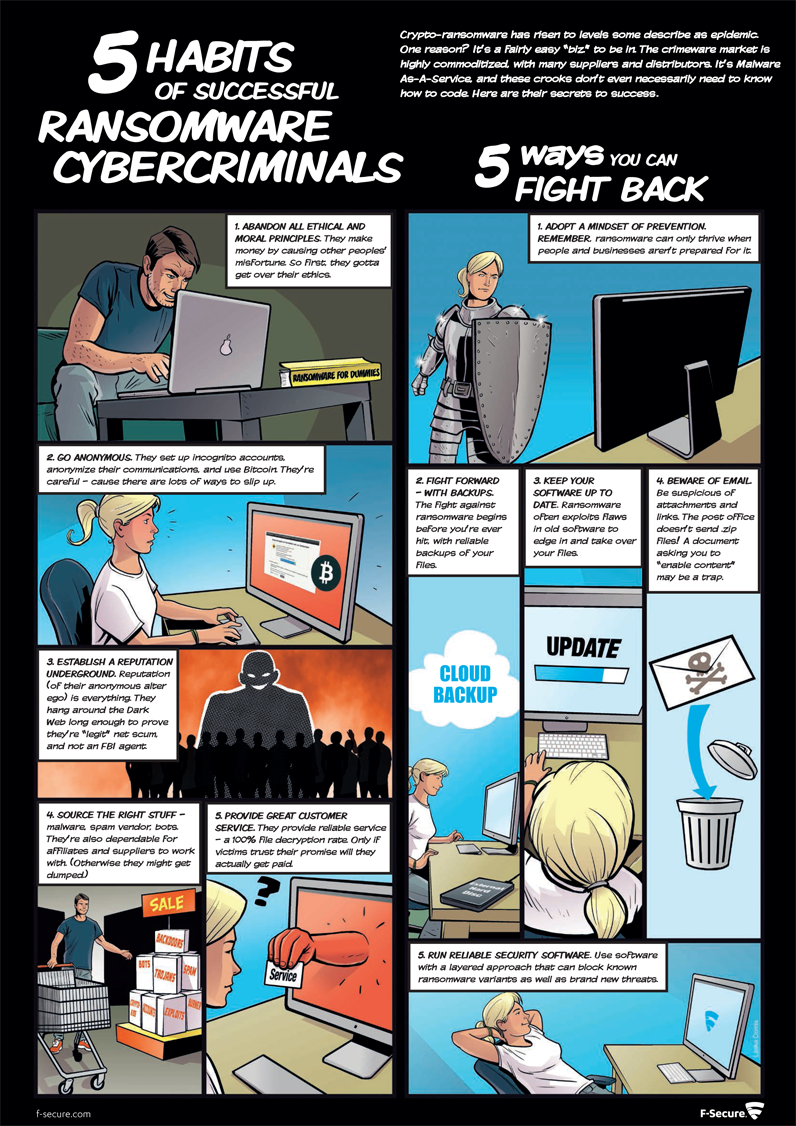
How to fight back against ransomware cybercriminals
‘Crypto-ransomware has risen to levels some describe as epidemic.’ In this nifty infographic, F-Secure outline the five habits of successful ransomware cybercriminals and how to fight back against their attacks.
The crimeware market is highly commoditised, with many suppliers and distributors. It’s Malware As-A-Service and these crooks don’t even necessarily need to know how to code. Here are their secrets to success:
5 Habits of successful Ransomware Cybercriminals
- Abandon all ethical and moral principles
- They make money by causing other peoples’ misfortune. So first, they’ve got to get over their ethics.
- Go anonymous
- They set up incognito accounts, anonymise their communications and use Bitcoin. They’re careful – because there are lots of ways to slip up.
- Establish a reputation underground
- Reputation (of their anonymous alter ego) is everything. They hand around the Dark Web long enough to prove that they are “legit” net scum and not an FBI agent.
- Source the right stuff
- Malware, spam vendor, bots. They’re also dependable for affiliates and suppliers to work with. (Otherwise they might get dumped.)
- Provide great customer service
- They provide reliable service – a 100 per cent file decryption rate. Only if victims trust their promise will they actually get paid.
Five ways you can fight back
- Adopt a mindset of prevention
- Remember, ransomware can only thrive when people and businesses aren’t prepared for it.
- Fight forward – with backups
- The fight against ransomware begins before you’re ever hit, with reliable backups of your files.
- Keep your software up to date
- Ransomware often exploits flaws in old software to edge in and take over your files.
- Beware of email
- Be suspicious of attachments and links. The post office doesn’t send .zip files! A document asking you to “enable content” may be a trap.
- Run reliable security software
- Use software with a layered approach that can block known ransomware variatns as well as brand new threats.
More from F-Secure
According to a recent experiment detailed in a new F-Secure report, Evaluating the Customer Journey of Crypto-Ransomware and the Paradox Behind It, Ransomware criminals actually care about your convenience! The experiment involved evaluating the “customer experience” of five current crypto-ransomware variants, beginning with the initial ransom screen all the way to interacting with the criminals behind each of those variants.
The report’s findings include:
- Those families with the most professional user interfaces are not necessarily also those with the best customer service.
- Crypto-ransomware gangs are usually willing to negotiate the price. Three out of four variants were willing to negotiate, averaging a 29 per cent discount from the original ransom fee.
- Ransomware deadlines are not necessarily “set in stone.” 100 per cent of the groups contacted granted extensions on the deadlines.
- One of the groups claimed to be hired by a corporation to hack another corporation – a kid playing a prank, or a sinister new threat actor?
To read the full report, visit: Report: Evaluating the Customer Journey of Crypto-Ransomware and the Paradox Behind It
[su_button url=”https://www.f-secure.com/en_GB/welcome” target=”blank” style=”flat” background=”#df2027″ color=”#ffffff” size=”10″ radius=”0″ icon=”icon: arrow-circle-right”]For more information on F-Secure click here[/su_button]